Look inside
Inspect content instead of guessing from filenames, with built-in patterns and customer-defined labels.
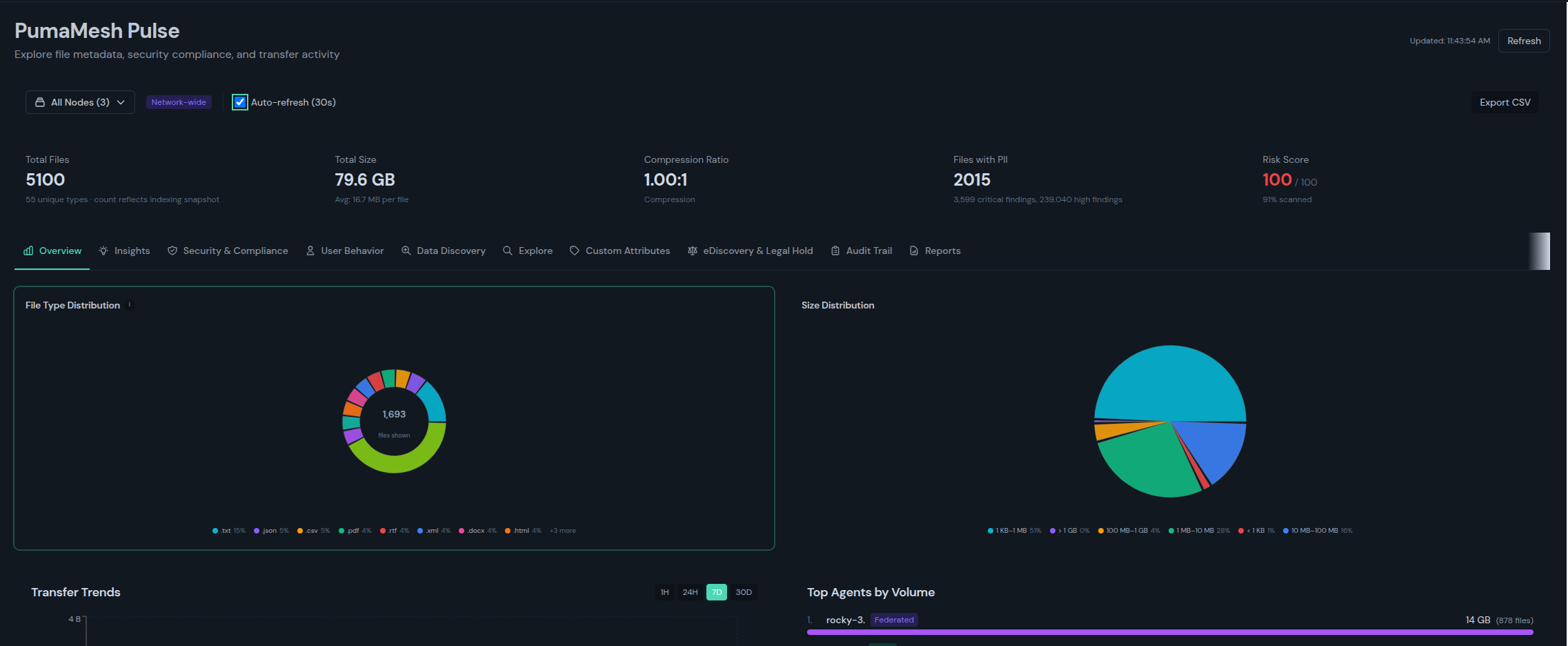
Pulse is the PumaMesh layer for visibility, findings, lineage, and evidence. It helps buyers know what data they have, how it moved, and what proof exists without sending teams to a separate analytics stack.
Use Pulse when the question is not just "did the file move?" but "what was it, who touched it, what policy applied, and can we prove it later?"
Pulse keeps discovery, policy, movement, and evidence connected. The first job is clarity: make sensitive data, risky movement, and audit proof visible in the same place operators already use.
Inspect content instead of guessing from filenames, with built-in patterns and customer-defined labels.
Connect findings to the compliance and AI governance frameworks buyers already need to explain.
Use content and user context to decide who can see, move, or act on data.
Turn findings into action and proof without exporting everything into a separate reporting project.
Pulse ships with 11 views, 15 report sources, 120+ sensitive-data patterns, and 10,000 attributes per file — all federated across the mesh without a central collector.
11 views
One federated layer for posture and evidenceOverview, Security & Compliance, UEBA, Data Discovery, Custom Attributes, eDiscovery, Audit Trail, Reports, System Metrics, Format Scanner, and AI Insights.
15 report sources
Operational and risk reports without a separate stackBuild reports from fifteen sources the platform already collects — findings, transfers, policy violations, storage, and more.
120+ patterns
Sensitive-data detection across the fabricFind PII, PHI, financial, credential, and cryptographic data — no file is opaque, no extra scanner required.
10,000 attributes
Rich metadata per fileEvery file can carry metadata that drives ABAC, reporting, search, and forensic review across the whole fabric.
Federated queries
Query local, all peers, or a custom setEvery view runs against the mesh directly. No central collector, no late-night ETL job.
6 visualizations
From summary to evidence fastTables, charts, metric cards, treemaps, and heat maps — built for operator dashboards and recurring reports.
Pulse is not just "discover and classify." It is a repeatable workflow: find exposure, rank risk, assign owners, fix it, and prove closure with exportable evidence.
Find Exposure
Start from sensitive data and operational contextSee findings, classifications, storage spread, exposure signals, and movement context across every node.
Rank Risk
Prioritize what actually mattersRisk score, anomaly views, confidence levels, and framework-mapped reports keep teams on the most urgent problems first.
Prove Closure
Keep evidence attached to the workflowAudit-ready reports, chain-of-custody, exportable artifacts, and case workflows make the response easy to review later.
Pulse maps to the posture language buyers already know — discovery, exposure, classification, anomaly, compliance, remediation — then extends it into motion and AI. And because it lives inside the fabric that moves the data, findings are immediately actionable.
Discovery
See sensitive data, exposure, and category contextKnow what the data is, where it sits, and which findings matter — before you move, restrict, or escalate it.
Insights
Coverage, confidence, and improvement over timeTrend and confidence views make posture work measurable instead of anecdotal.
DSPM Fit
Maps cleanly to the posture language buyers knowSix posture categories familiar to any DSPM evaluator — extended into transfers and AI pipelines, federated by default.
Investigation Fit
Pulse leads with evidenceTimeline, source-linked findings, identity and activity context, and exportable reports make Pulse credible for early-stage investigation.
Differentiator
Analytics tied to movement and policyOne data model for transfer, posture, and audit — findings drive policy, not just dashboards, and are actionable in the same console.
Programmatic Access
Scoped API tokens with expiry and revocationReach Pulse data and collection workflows through scoped, revocable tokens — so reporting automates cleanly into your existing tools.
Case lifecycle, legal hold, collection search, and chain-of-custody are built in — integrated workflows inside the fabric, not a replacement for a full downstream review suite.
Legal Hold
Preserve data in place, across the meshPlace holds on files wherever they live — hubs, relays, or agents — without moving the data first.
Collection Search
Find responsive data across the fabricFederated search with classification, attribute, and custody filters — scoped to the matter at hand.
Chain of Custody
Exportable evidence with provenanceEvery action is logged. Every artifact carries its custody record. Reports export in formats counsel and regulators accept.
Every major AI platform ships its own guardrails. None federate. When a sensitive record leaves a bucket, rides a transfer, lands in a fine-tune, and gets pulled by an agent tool-call on another platform, Pulse is the only place the full path is visible.
Prompt + Retrieval Lineage
Link prompts and responses back to source-row sensitivityTie RAG retrievals, fine-tune inputs, and agent tool-calls back to the original classified records — across platform boundaries.
Fine-Tune Leakage
See which sensitive data entered which modelTraining set posture, fine-tune provenance, and model lineage — the governance layer MLOps platforms still don't own.
Agent Tool-Call Policy
Enforce ABAC on what agents can reachThe same attributes that gate file movement also gate what AI agents can read, write, and act on through tool-calls.
Pulse helps teams see exposure faster, connect identity and activity, prioritize fixes, govern AI pipelines, and produce audit-ready evidence — all from one federated layer.
DSPM
Discovery, exposure, posture, and risk reportingMatches the language of Cyera, Sentra, Varonis, BigID, Rubrik, and Proofpoint — then extends it into motion and AI.
DSPM for AI
Federated lineage across AI platformsThe white space no AI platform vendor owns: one neutral posture view across Bedrock, Foundry, Vertex, Databricks, Snowflake, and the data feeding them.
eDiscovery
Legal hold, collection, chain of custody, and reportingIntegrated investigation workflows inside the platform — not a replacement for a full downstream review suite.