Protect
Keep encryption, access control, and audit in the same workflow so sensitive data is protected in motion and at rest from the start.
PumaMesh helps buyers replace brittle file-transfer stacks with one platform that protects data, explains what it is, moves it across hard environments, and keeps proof ready without extra add-ons.
The same operating model runs across Windows and Linux, uses Hub, Relay, and Agent roles where they fit, and keeps policy, audit, and encryption in the path.
PumaMesh gives teams one operating model: protect important data, understand what it is, move it where it belongs, and accelerate access without stitching together separate transfer, security, and evidence products.
Keep encryption, access control, and audit in the same workflow so sensitive data is protected in motion and at rest from the start.
Classify and label data where it already lives so teams know what they are moving and how it should be governed before it leaves the source.
Use the same platform across Windows, Linux, partners, cloud, and edge with Hub, Relay, and Agent roles that keep policy attached to every transfer.
Give operators faster access, better visibility, and benchmarked performance so data teams can act quickly without trading away proof.
The same fabric answers security, AI platform, and compliance conversations without splitting the deployment into separate products.
CISO · Security Leadership
MOVEit-class zero-days, quantum migration deadlines, audit fatiguePain: Java runtimes shipped the 2023 MFT zero-days. CNSA 2.0 migration starts now. Every framework wants its own audit.
Outcome: Memory-safe single binary, post-quantum by default, one tamper-evident audit chain that exports to CMMC, FedRAMP, HIPAA, and EU AI Act simultaneously.
Platform · AI Engineering Lead
70B models don’t move on 20-year-old transportsPain: Legacy MFT is Linux-only. File-sharing tools don’t do line rate. Every app needs a new SDK integration.
Outcome: 25.8 Gbps sustained across 135 ms RTT. Native Windows and Linux agents. Applications keep using normal file paths — crypto and policy are transparent.
Compliance Officer · Program Manager
CMMC, FedRAMP, EU AI Act, NIST AI RMF, ISO 42001 — one chainPain: Every framework wants its own evidence artifact. Legacy stacks produce five separate audit chains that never reconcile.
Outcome: All 110 CMMC controls met for data sharing. FedRAMP-aligned. wolfSSL 5.9.1 in the cryptographic stack. Evidence is a byproduct, not an after-the-fact project.
Every node is a peer. The Hub coordinates policy and visibility, the Relay bridges hard networks, and the Agent runs where data lives.
Hub · Linux
Policy, orchestration, and fabric-wide visibilityThe control plane for the mesh. Hubs distribute policy, manage keys, and give operators one view of fabric health.
Agents keep running even when the Hub is unreachable — peers continue to move data under the last known policy.
Relay · Linux
Extend the mesh across remote, air-gapped, and intermittent networksFor disparate networks, B2B exchange, and trust boundaries where direct peer links can't reach.
Pure encrypted passthrough — no plaintext, no disk staging. The mesh reroutes automatically if any relay drops.
Agent · Linux & Windows
Every endpoint becomes an autonomous peerSecurity should begin at the creation or capture of data.
The Agent runs wherever data lives — endpoints, sensors, VMs, cloud instances — and classifies, encrypts, enforces policy, and moves data at the source.
At rest, every file gets transparent protection. In flight, every stream runs through the post-quantum mesh. Applications keep using normal paths and APIs. See the Mesh for transport, crypto, and routing →
Transparent PQ Encryption
Post-quantum protection the applications never seeData is encrypted and identity-bound the moment it enters the fabric. Users and applications keep using normal file paths and APIs — no SDK to integrate, no certificates to manage per app, no workflow change.
Shield + Audit
Protection is part of the data pathCertificate and key lifecycle, per-file audit trail, and operator action logs sit next to the transfer — not in a separate security product.
ABAC
Attribute-based access control — content decides accessRegex finds keywords inside every file — classification markers, PII patterns, project codes, customer identifiers. Those keywords become attributes on the file. Every user identity carries its own attribute set. Access is granted only when the identity's attributes match the file's. No match, no access — on every transfer, every retrieval, and every tool-call.
Policy Detail
File context becomes enforceable rulesThe attributes used for reporting and discovery also drive who can see files and where they can go. One attribute surface, many enforcement points.
PumaMesh inspects files where they live, turns findings into signed attributes, and uses those attributes for search, policy, and reporting. Sensitive-data patterns, customer ontologies, ABAC, and framework mapping share one evidence surface.
Find
Distributed search across the meshOperators search across local and remote nodes, filter by classification, and act on files with full sensitivity context.
Classification
PII, PHI, and custom attribute contextBuilt-in patterns and custom attributes make every file legible — no more moving opaque bytes across the network.
Metadata
Rich metadata powers policy and reportingAttribute distribution and metadata density show operators what policy can enforce before the file moves.
Machine to machine, machine to person, and person to person movement all run through the same policy, encryption, and audit surface. Native Windows and Linux agents carry the fabric from laptops to GPU clusters, edge sites, and partner environments.
Speed
Line-rate transfer over distanceSustained throughput across long-haul, degraded, and constrained links — the WAN stops being the reason data waits. Always-on compression gets even more out of every link.
Goodput
What arrives, not just what was sentResilient, loss-tolerant movement that holds steady under jitter, packet loss, and path changes. The number on the dashboard is the number that lands.
Attribute-Based Routing
Policy decides where data is allowed to travelNodes carry labels. Data carries labels. The fabric compares the two and routes accordingly — so a classified payload never reaches an unauthorized location, regardless of how the peers are deployed.
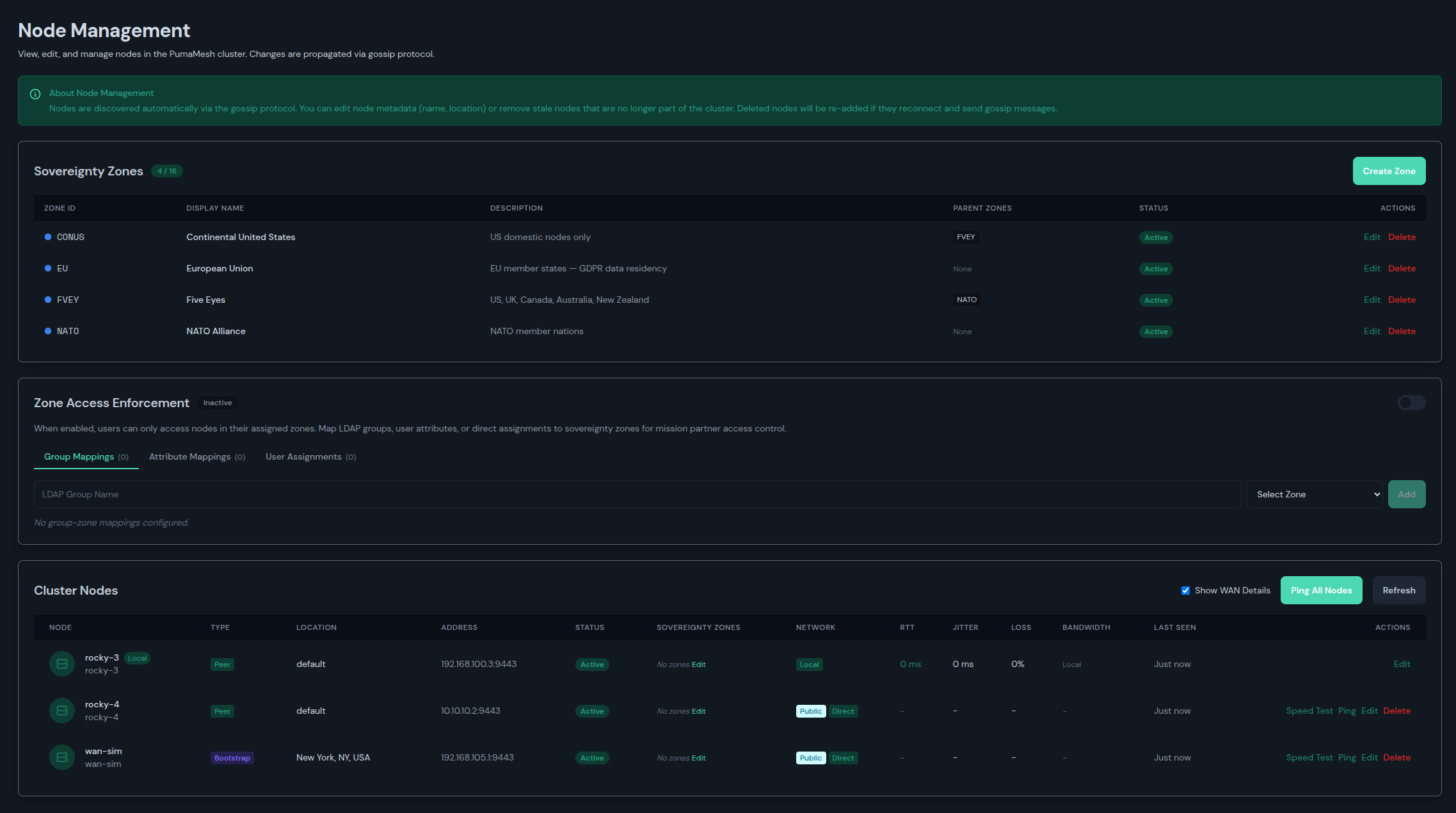
Zones Extend ABAC
Location becomes part of the policy surfaceSovereignty zones restrict what can be sent where, by geography and trust boundary — a location attribute that stacks on top of ABAC rules written for the data itself.
PQ Mesh Underlay
Every peer link is post-quantum-protectedPeer-to-peer transport with identity-bound, post-quantum encryption on every hop. The network itself is the trust boundary — not a gateway in the middle.
Operator Visibility
Direction, throughput, duration, and endpoint contextEvery transfer shows up with full context in the same console that runs it — so operators can see what moved, how fast, and which policy applied.
Acceleration is not only throughput. It is faster access, faster insight, and faster evidence because the data, policy, classification, movement, and audit trail all live in the same fabric.
Time to Access
Find the data wherever it lives — no staging copiesFederated search across every peer means the nearest authorized copy answers the query. No central collector to populate, no ETL job to wait on, no "please copy that to my region first."
Time to Insight
Context arrives with the dataClassification, findings, and attributes travel alongside the transfer. The moment data lands, it is already legible to policy, search, and analytics — the answer doesn't wait on a downstream pipeline.
Time to Decision
Evidence ready the moment it is neededLineage, audit, and chain-of-custody are a byproduct of doing the work — so investigation, compliance review, and operator action happen in minutes, not weeks of post-processing.